Cryptosystem ME6 |
|
Cryptosystem ME6 |
|
This software runs on any version of Windows. It is fully-functional and not time-limited.
Donate via Stripe to download this software.
Some features of Cryptosystem ME6:
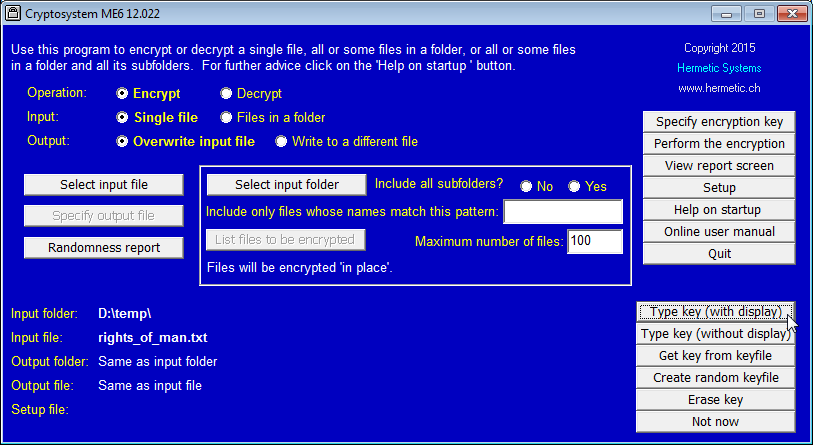
Here is a typical screenshot:
|
The Cryptosystem ME6 Encryption Process Cryptosystem ME6: Statistical Tests and An Introduction to the Use of Encryption |
Dr Aiko Pras, of the University of Twente's Design and Analysis of Communication Systems group, said on May 29, 2013: "[An] interesting development is the cloud: everyone stores all sorts of documents there, but no-one considers that all these files eventually end up in the United States. You can depend on it that the American authorities [NSA] — and soon the Chinese — will be reading them."
"Microsoft has collaborated closely with US intelligence services to allow users' communications to be intercepted, including helping the National Security Agency to circumvent the company's own encryption, according to top-secret documents obtained by the Guardian. ... The documents show that the company worked with the FBI this year to allow the NSA easier access via Prism to its cloud storage service SkyDrive, which now has more than 250 million users worldwide."
So if you store confidential data in the cloud then it's highly advisable to encrypt it before uploading.
In January 1999, the Defense Research and Development Organization (DRDO) [of India] issued a 'red alert' against all network security software developed in the US. ... Specifically, the DRDO is concerned about U.S. "encryption software products" that can be 'broken' by the NSA. The agency pointed out "no encryption software products can be exported from the U.S. if they are too strong to be broken by the U.S. National Security Agency." ... The letter says: "To put it bluntly, only insecure software can be exported. When various multinational companies go around peddling 'secure communication software' products to gullible Indian customers, they conveniently neglect to mention this aspect of the U.S. export law." — Cryptography and Liberty 1999: An International Survey of Encryption Policy
Cryptosystem ME6 was designed and developed in Europe. Thus it was not designed (as most commercial U.S.-developed encryption software is) to be sufficiently weak to qualify for a U.S. export license. On the contrary, it was designed to be as strong as possible. This file encryption software has no backdoor, and the encryption key is not hidden in the ciphertext. (The encryption algorithm is described at The Cryptosystem ME6 Encryption Process.)