Email Encryption End‑to‑End | ||
Encryption software for secure end‑to‑end transmission of email | ||
Email Encryption End‑to‑End | ||
Encryption software for secure end‑to‑end transmission of email | ||
This software runs on any version of Windows. It is fully-functional and not time-limited.
Donate via Stripe to download this software.
|
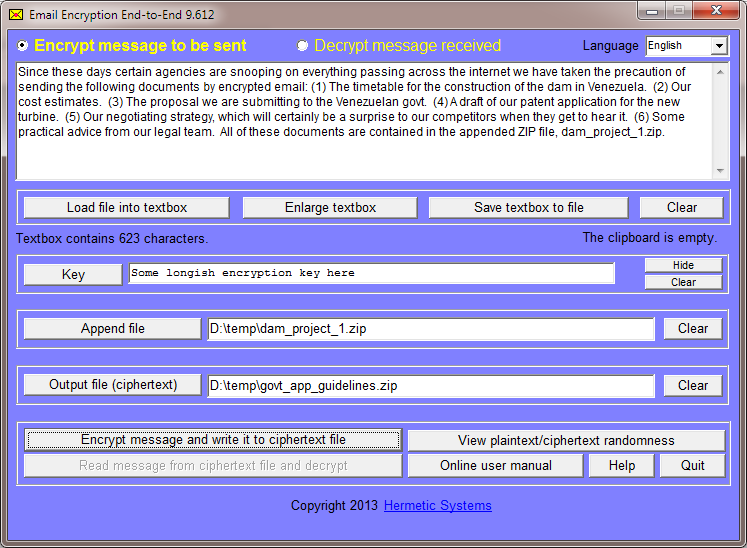
Here is a sample screenshot just prior to encrypting a message: |
|
| |
Email Encryption End‑to‑End makes it easy to send and receive encrypted email. It can be used to encrypt a message to be sent via any desktop email program or webmail that supports attachments (that is, files attached to a message). The encrypted message consists of a text message (up to 60 KB in size) plus, optionally, an appended file of any type (up to 1,980 KB = 1.93 MB in size). The message (including any appended file) is encrypted and written to a ciphertext file. You then attach this file to an ordinary email message. Thus your message is encrypted before it leaves your PC to go to the mail server, and it remains encrypted during transmission to the recipient's ISP and while being downloaded to the recipient's PC. Thus the message is encrypted "end‑to‑end", and, if intercepted anywhere between your PC and the recipient's PC, cannot be read.
| User Manual | ||
|
Use of the Program Specifying the Encryption Key Comparing Plaintext and Ciphertext for Randomness The Encryption Method |
||