Crypto and Privacy Links |
Crypto and Privacy Links |
The fallout from the Wikileaks' "Vault 7" release this morning of thousands of documents demonstrating the extent to which the CIA uses backdoors to hack smartphones, computer operating systems, messenger applications and internet-connected televisions, will be profound.
The Identity Project explores and defends the fundamental American right to move freely around our country and to live without constantly having to prove who we are or why we are here.
Pegasus is different from normal phone or physical surveillance because it offers complete and irreversible control of the target's phone. ... The key-logger built into the spyware saves the usernames and passwords of other sensitive accounts operating from the infected device. This allows for the sending of emails and even the planting of false evidence in the target's Google account.
Speech recognition technologies can identify and tag individuals every time they open their mouths [and say something], effectively ending anonymity.
You can also download older versions of the Audacity program for now that do not have "phone home" functionality. Or if you have read the privacy policy and don't mind the terms, you can keep using the main release. This change just puts Audacity in line with countless other apps that harvest your data.
A personal digital assistant (PDA) is a portable electronic device used for personal organization and communication. ... For years concern has been growing over the ability of such devices to spy on us in the privacy of our homes and offices. ... This monster is the child of governments and technology and its goal is to grow more powerful. By convincing us that technology and robots will add quality to our lives they are seducing a weak-minded population into submission. When we surrender control of our lives to those and the forces that gain from our compliance we would be wise to remember we are at their mercy. ... [This] means if and when people attempt to take back control over their lives it will be almost impossible.
However, users outside the US will be able to manually turn the feature on by heading into Settings, General, and then scrolling down to Networking Settings.
Was it CIA or NSA? See Wayne Madsen's Crypto AG: The NSA's Trojan Whore?, an article published in 2001 or earlier, which does not mention the CIA.
Social media companies may soon be forced to allow backdoor government access to encrypted information.
Every minute of every day, everywhere on the planet, dozens of companies — largely unregulated, little scrutinized — are logging the movements of tens of millions of people with mobile phones [including yours] and storing the information in gigantic data files. ... Each piece of information in [these files] represents the precise location of a single smartphone [such as yours] over a period of several months [or years] ... You've probably never heard of most of the [location tracking] companies — and yet to anyone who has access to this data, your life is an open book. They can see the places you go every moment of the day, whom you meet with or spend the night with, where you pray, whether you visit a methadone clinic, a psychiatrist's office or a massage parlor.
And perhaps to cities in Western Europe and the U.S. also — they're just not telling us about it, whereas Huawei is open about it (until they're censored by the local government) because they want to sell their product.
So have they stopped?
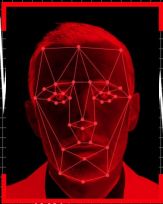
Deciding where to draw the line between [privacy and security] is key. But we also have to make the decision clearly and explicitly. At the moment there is a great risk that as the use of facial recognition technology by government and business spreads, the decision will be taken away from us.
How can it "be taken away" if "we" never had it? The only way to avoid living in a total surveillance state is to live in a country which does not have several surveillance cameras on every city block.
The bug, if exploited, can escalate a local unprivileged user to the full "system" level rights — granting them access to every corner of the operating system. But Microsoft, which owns the voice- and video-calling service, said it won't immediately fix the flaw, because the bug would require too much work.
 Ryan Gallagher & Ludovica Jona: We Tested Europe’s New Lie Detector for Travelers — and Immediately Triggered a False Positive
Ryan Gallagher & Ludovica Jona: We Tested Europe’s New Lie Detector for Travelers — and Immediately Triggered a False Positive
Ray Bull, professor of criminal investigation at the University of Derby, has assisted British police with interview techniques and specializes in methods of detecting deception. He told The Intercept that the iBorderCtrl project was “not credible” because there is no evidence that monitoring microgestures on people’s faces is an accurate way to measure lying. “They are deceiving themselves into thinking it will ever be substantially effective and they are wasting a lot of money,” said Bull. “The technology is based on a fundamental misunderstanding of what humans do when being truthful and deceptive.”
If implemented, this system will result in many innocent travelers being unjustly denied entry to the EU. But why should the EU bureaucrats care?
It won’t be long before we find ourselves looking back on the past with longing, back to an age where we could speak to whom we wanted, buy what we wanted, think what we wanted without those thoughts, words and activities being tracked, processed and stored by corporate giants such as Google, sold to government agencies such as the NSA and CIA, and used against us by militarized police with their army of futuristic technologies. To be an individual today, to not conform, to have even a shred of privacy, and to live beyond the reach of the government’s roaming eyes and technological spies, one must not only be a rebel but rebel.
Time to get out of the city.
A low social credit score will exclude you from well-paid jobs, make it impossible for you to get a house or a car loan or even book a hotel room. The government will slow down your internet connection, ban your children from attending private schools and even post your profile on a public blacklist for all to see.
... they were able to use a tiny sample set of 10 minutes of audio in order to create a synthesized voice of a target, and spoof their voice using text-to-speech. That was enough, in many cases, to fool voice authentication systems and access a protected account.
Something to think about when a government agent insists that you phone them on some matter.
Facebook is not only watching, but also listening to your cell phone. It all starts with enabling your microphone feature in your settings. Once you do, choose your words carefully.
The Australian Parliament passed a contentious encryption bill on Thursday to require technology companies to provide law enforcement and security agencies with access to encrypted communications. Privacy advocates, technology companies and other businesses had strongly opposed the bill, but Prime Minister Scott Morrison’s government said it was needed to thwart criminals and terrorists who use encrypted messaging programs to communicate. ... Opponents of the bill argued that it not only compromised Australians’ privacy but was vaguely written in a way that could lead to abuses. They also said it was being rushed through Parliament without proper consultation with the public.
The Boston Globe has revealed a new federal program that profiles and surveils ordinary US citizen travelers who otherwise have no legitimate reason for being profiled [and watched]. ... In essence, the program gives the TSA the option to monitor and track whoever it likes for any reason whatsoever, effectively granting TSA agents a green light to violate anyone's personal privacy ...
The Intel Management Engine [ME] with its proprietary firmware has complete access to and control over the PC: it can power on or shut down the PC, read all open files, examine all running applications, track all keys pressed and mouse movements, and even capture or display images on the screen. And it has a network interface that is demonstrably insecure, which can allow an attacker on the network to inject rootkits that completely compromise the PC and can report to the attacker all activities performed on the PC. It is a threat to freedom, security, and privacy that can't be ignored. ... [The ME] and its applications are a backdoor with total access to and control over the rest of the PC. The ME is a threat to freedom, security, and privacy, and the libreboot project strongly recommends avoiding it entirely. Since recent versions of it can't be removed, this means avoiding all recent [later than 2009] generations of Intel hardware.
Before going into customs, alert a lawyer or a loved one who can contact a lawyer, and contact them again when you get out. If you are detained, you may not be able to access your devices or otherwise have the opportunity to reach the outside world. And in the worst case scenario of a lengthy detention, you'll want someone advocating for your release and legal representation.
One commenter says:
"MAY" be right? Of course it's right. It's how the NWO was intended to be built. Interlocking secrets/scandals/pedophilia/blackmail on one another's leadership with the bankers jerking the puppet strings. Creates a net of controlled corruption extending transnationally with consequent treasonous conduct in each of one another's countries collapsing them into cesspools of decaying stinking corruption. It's how they, the bankers, squash national allegiences among leaders so corrupted by promising to "save" them from domestic prosecution for their crimes.
Yahoo Inc last year [2015] secretly built a custom software program to search all of its customers' incoming emails for specific information provided by U.S. intelligence officials ...
[Thales] has the French state as a major shareholder. ... "Today, it’s testing at the border, tomorrow it could be facial recognition deployed in public places," Dave Maass, Electronic Frontier Foundation, said. "Today, the photos taken are being kept segregated from other departments and agencies, tomorrow they could be shared for a whole host of other purposes."
However, everyone has "something to hide". Why do you think that your bank encrypts your data when you use online banking? To assist the FBI in "keeping us safe", would you rather that banks stopped encrypting everyone's data (including your own)?
Although “the legislative environment is very hostile today,” the intelligence community’s top lawyer, Robert S. Litt, said to colleagues in an August e-mail ... “it could turn in the event of a terrorist attack or criminal event where strong encryption can be shown to have hindered law enforcement.” ... What is clear, though, is that the law enforcement argument is “just not carrying the day,” said a second senior official ... “People are still not persuaded this is a problem. People think we have not made the case. We do not have the perfect example where you have the dead child or a terrorist act to point to, and that’s what people seem to claim you have to have.”
So get ready for another false-flag "terrorist attack".
Nobody is saying the obvious: cracking encryption to steal data is unconstitutional and illegal and this debate is taking place at a moment when massive movements of protest are convering the streets of our cities organized through social media and cell-phone communications. ... Both the First and Fourth Amendments to the Constitution make absolutely clear that the government cannot do mass data capture. There is no fuzziness about that in the document’s wording. Data from citizens can only be captured with a court-approved search warrant and then only when the object of the data seizure is specifically described in the warrant. ... Privacy, the constitutional principle written to protect movements and citizen organizing (among other things), has been washed down the legal drain. The only protection we have is to encrypt what we send and constitutionally we have an absolute right to do so.
The Greens senator Scott Ludlam said the last-minute amendments to protect journalists “did nothing to protect the 23 million other Australians who will still be exposed to out of control warrantless surveillance”.
U.S. and British spies hacked into the world's biggest maker of phone SIM cards [Gemalto], allowing them to potentially monitor the calls, texts and emails of billions of mobile users around the world, an investigative news website reported.
In a speech today in Strasbourg opening the current session of the European Parliament, the President of the European Council (the executive branch of the European Union, comprised of national governments) invoked the attack on the satirical cartoonists of Charlie Hebdo as a reason for popularly-elected EU legislators to put aside their previous objections and enact a comprehensive EU-wide mandate for surveillance and profiling of airline passengers on the basis of Passenger Name Record (PNR) data from airline reservations.
US government-owned airplanes that can cover most of the continental United States are covertly flying around the country, spying on tens of thousands of innocent people’s cellphones. It sounds like a movie plot, but in a remarkable report published on Thursday, the Wall Street Journal exposed that these spy planes are part of an actual mass surveillance program overseen by the Justice Department (DOJ). And it’s been kept secret from the public for years.
At the heart of the expanded effort is a database called the Automated Targeting System ... [which] is used to decide who is placed on the no-fly list — thousands of people the United States government has banned from flying — and the selectee list, an unknown number of travelers who are required to undergo more in-depth screening ... The T.S.A. also maintains a PreCheck disqualification list, tracking people accused of violating security regulations, including disputes with checkpoint or airline staff members. Much of this personal data is widely shared within the Department of Homeland Security and with other government agencies ... and in some cases, [with] private companies for purposes unrelated to security or travel.
The National Security Agency has obtained direct access to the systems of Google, Facebook, Apple and other US internet giants, according to a top secret document obtained by the Guardian. The NSA access is part of a previously undisclosed program called PRISM, which allows officials to collect material including search history, the content of emails, file transfers and live chats, the document says.
The National Security Agency is currently collecting the telephone records of millions of US customers of Verizon, one of America's largest telecoms providers, under a top secret court order issued in April. ... Under the terms of the blanket order, the numbers of both parties on a call are handed over, as is location data, call duration, unique identifiers, and the time and duration of all calls. The contents of the conversation itself are not covered.
But at the very least they can know who you're calling and they can track your movements. Whenever you switch on your cellphone they know instantly where you are.
[Some rich people who hide their money to avoid paying taxes on it] are suddenly very anxious after the leak of 2.5 million files detailing the offshore bank accounts and shell companies of wealthy individuals and tax-averse companies. ... [The] the enormous size of the data dump obtained by the International Consortium of Investigative Journalists ... has punched a big hole in the secrecy that surrounds what the Tax Justice Network estimates are assets worth at least $21 trillion held in offshore havens.
In the United States, providing government law enforcement with back-door access to networks, aka 'lawful intercept', is a legal requirement for digital telecom, broadband Internet, and voice-over-IP service and equipment providers under the CALEA (Communications Assistance to Law Enforcement Act) law. The Federal Bureau of Investigation (FBI) is currently lobbying the US administration and the Federal Communications Commission to require that social-media providers such as Facebook provide similar access so that chats and instant messaging can also be monitored in real time or extracted from digital storage.
The Australian government has proposed sweeping changes to its surveillance and national security laws. The government's wish list includes mandatory data retention, surveillance of social networks, criminalization of encryption, and lower thresholds for warrants.
Under the guise of expanding "the fight against terrorism" the Australian spooks wish to "establish an offence for failure to assist in the decryption of communications". So if you have some proprietary commercial information which you encrypt and send in a file to a colleague, and if you refuse a request by the Australian government to allow them to decrypt that file, then you can be charged with the commission of a crime (proposed penalty as yet unstated but could be imprisonment).
A federal domestic security effort to help state and local law enforcement catch terrorists by setting up more than 70 information-sharing centers around the country has threatened civil liberties while doing little to combat terrorism, a two-year examination by a Senate subcommittee found.
And here is a link to the report itself.
Offensive cyber-tactics fall into five basic categories: using the Internet to win hearts and minds; denial of service attacks that effectively paralyze websites; electronic attacks on infrastructure such as nuclear power plants; sabotage through the sale of defective hardware or software; and operational attacks that accompany conventional battle plans ...
TThe purpose of the NSA's "Utah Data Center" is "to intercept, decipher, analyze, and store vast swaths of the world’s communications as they zap down from satellites and zip through the underground and undersea cables of international, foreign, and domestic networks. ... Flowing through its servers and routers and stored in near-bottomless databases will be all forms of communication, including the complete contents of private emails, cell phone calls, and Google searches, as well as all sorts of personal data trails — parking receipts, travel itineraries, bookstore purchases ...
There’s a new trend in social media and application development, and it’s called ‘social discovery’.
"Meema" commented:
The one thing social networking is NOT about, is “giving” people opportunities to connect better, unless that means better opportunity for exposure to product and data gathering by government. Once upon a time there were phone calls and actual face to face connecting. And then along came email which made it possible to connect quickly and cheaply with those who were far away and did that very well actually but unfortunately there was no place for marketing in private email exchanges so email had to be replaced.Here’s my stand, I choose NO, so I don’t do Facebook, Twitter or any online social networking site because I know what the true purpose is, i.e., harvesting target info. I discourage my clients from this as well. Amazingly I survive quite well without being “connected” or “liked” and I am quite sure there is plenty of information about me available anyway. I’m such a relic I do my interacting the old fashioned way with people I have intimate relationships; I communicate one on one, face to face, by phone and the now archaic tool of email. There is no substitute for this kind of interaction with humans. None. It seems to me that the more knowledge has increased, the more information we have, the less we really know because not only has the human touch thing been circumvented by digital technology, humanity itself is now systematically being counterfeited with a shallow reproduction. We are becoming programed holograms. The real deal, that unique part of humanity that has always been delightfully serendipitous, has now been replaced with a robotic, predictable, never allowed to step sideways, soul-less clone that lives for, acts and reacts, and by default witlessly worships, the god of commerce.
[Soon] it will become technologically and financially feasible for authoritarian governments to record nearly everything that is said or done within their borders — every phone conversation, electronic message, social media interaction, the movements of nearly every person and vehicle, and video from every street corner. Governments with a history of using all of the tools at their disposal to track and monitor their citizens will undoubtedly make full use of this capability once it becomes available.
[Security researcher Trevor] Eckhart said he'd discovered Carrier IQ's software secretly monitoring “many U.S. handsets sold on Sprint, Verizon, and more.” He estimated that it was running on more than 141 million handsets. Furthermore, as installed by carriers, the software oftentimes couldn't be removed, or could be removed only by advanced users willing to root their phones.
Federal Customs and Border Patrol agents have the [legal] right [according to the 9th Circuit Court in San Francisco] to confiscate and examine electronic devices belonging to anyone entering the United States. The agents aren't required to have probable cause before searching someone's devices. And they can look for any evidence of any crime at all.
The procedures also allowed border agents to retain documents and devices for 'a reasonable period of time' to perform a thorough search 'on-site or at an off-site location.'
So if you enter the U.S. with a laptop you can expect federal agents to look through your personal files and maybe even take your laptop away for a few hours or days and perhaps even copy the entire hard drive. Better to stay far away.
The Electronic Communications Privacy Act ... is a patchwork of confusing standards that have been interpreted inconsistently by the courts, creating uncertainty for both service providers and law enforcement agencies. ECPA can no longer be applied in a clear and consistent way, and, consequently, the vast amount of personal information generated by today's digital communication services may no longer be adequately protected.
that are prohibited by governments worldwide, in particular material on freedom of expression, privacy, cryptology, dual-use technologies, national security, intelligence, and secret governance -- open, secret and classified documents -- but not limited to those. Documents are removed from this site only by order served directly by a US court having jurisdiction. No court order has ever been served ...
This paper covers how DNS works: first at a high level, then by picking apart an individual packet exchange field by field. Next, we'll use this knowledge to see how weaknesses in common implementations can lead to cache poisoning.
In an interview Tuesday [2007-11-06], he [Mark Klein] said the NSA set up a system that vacuumed up Internet and phone-call data from ordinary Americans with the cooperation of AT&T. Contrary to the government's depiction of its surveillance program as aimed at overseas terrorists, Klein said, much of the data sent through AT&T to the NSA was purely domestic.
Radio tags used in everything from building access cards to highway toll cards to passports are surprisingly easy to copy and pose a grave security risk, researchers said this week."At security conferences researchers demonstrated that passports equipped with radio frequency identification (RFID) tags can be cloned with a laptop equipped with a $200 RFID reader and a similarly inexpensive smart card writer. In addition, they suggested that RFID tags embedded in travel documents could identify US passports from a distance, possibly letting terrorists use them as a trigger for explosives.
AT&T provided National Security Agency eavesdroppers with full access to its customers' phone calls, and shunted its customers' internet traffic to data-mining equipment installed in a secret room in its San Francisco switching center, according to a former AT&T worker cooperating in the Electronic Frontier Foundation's lawsuit against the company.
Think Bush's warrantless NSA surveillance is bad? Wait till you hear what the British government does.
The Stop Badware Coalition will seek to spotlight companies that make millions of dollars by tricking Web users into putting spyware, adware or other deceptive software on their machines ...
An antiterror law makes Internet cafe managers check their clients' IDs and track the websites they visit.
Recent developments in computer vision, robotics, and pattern matching increase the possibility of drastic social transformations. The dictatorship of Big Brother had one small limitation of power: it depended on the obedience and vigilance of subordinates to enforce control. The application of data mining methods to massive video data sets enables a sufficiently organized power to outmatch humans in carrying out surveillance.
Last week researchers at the Internet Storm Centre discovered a malicious program that used a flaw in the [Internet Explorer] software to install itself on the user's PC when a particular pop-up ad appeared. It would then monitor the user's typing when they visited any of 50 bank sites, including Barclays Bank, Citibank and Deutsche Bank.
Accenture and its partners will need to link the vast amounts of data that biometric devices capture with legacy databases of immigration, customs, law-enforcement, and intelligence agencies. ... it also will need to analyze data to spot suspicious activities.
To help counteract counterfeiting of the new currency, the EU is hoping to have a new RFID [radio frequency identification] tagging system in place by 2005. Each piece of currency will have a tag with a unique code which should be irreproducible by counterfeiters. ... [T]his also means that the governments would also be able to track the money when it is not being used in illegal transactions. This would mean that any money you had in your possession could be used to track you, no matter which EU country that you were in.
[Dean] called for state drivers' licenses to be transformed into a kind of standardized national ID card for Americans. ... Dean also suggested that computer makers such as Apple Computer, Dell, Gateway and Sony should be required to include an ID card reader in PCs — and Americans would have to insert their uniform IDs into the reader before they could log on.
Republican staff members of the US Senate Judiciary Commitee infiltrated opposition computer files for a year, monitoring secret strategy memos and periodically passing on copies to the media ...
Washington has requested non-U.S. airlines to hand over up to 39 pieces of data for each passenger, including credit card details, home address and phone number.
The key comment in Mr Bolkestein's statement is that the Commission has made its 'political judgement' in favour of transfer in the hope that any privacy problem will be in the meantime resolved. In short, the statement should be seen as a mechanism to boot the privacy problems into the long grass whilst allowing the US authorities access to the data they want.
Your Microsoft Word document can give readers more information about you than you might think.
If concerned, open your MS Word document with a text editor such as Notepad, which shows everything.
Another reconnaissance project involving submarines ... involved implanting a device to intercept the signals transmitted along a Soviet underwater cable in the Sea of Okhotsk, between the Kamchatka Peninsula and the eastern Soviet coastline. A combined Navy-NSA team, operating from a submarine, installed a miniaturized waterproof eavesdropping device — a large tape pod that fit over the Soviet cable, through which key Soviet military and other communications flowed. The pod had a wraparound attachment that intercepted the cable traffic by "induction" ... The Sea of Okhotsk operation continued until 1981, when former NSA employee Ronald Pelton sold the Soviets information about the operation.
TA website "designed to help you understand the basics of cryptography ... [and to provide] access to a series of resources to help you apply, and implement, cryptographic solutions.
Without any official public notice, and without any congressional hearings, the Bush administration — with an initial appropriation of $200 million — is constructing the Total Information Awareness System. It will extensively mine government and commercial data banks, enabling the FBI, the CIA, and other intelligence agencies to collect information that will allow the government ... 'to essentially reconstruct the movements of citizens.' This will be done without warrants from courts, thereby making individual privacy as obsolete as the sauropods of the Mesozoic era.
[A] Pentagon research agency ... considered but rejected ... tagging Internet data with unique personal markers to prevent anonymous use of some parts of the Internet. ... The plan, known as eDNA ... would have divided the Internet into secure 'public network highways' where a user would need to be identified, and 'private network alleyways' which do not require identification. ... [The proposal] read in part: 'We envisage that all network and client resources will maintain traces of user eDNA so that the user can be uniquely identified as having visited a Web site, having started a process or having sent a packet. 'This way, the resources and those who use them form a virtual 'crime scene' that contains evidence about the identity of the users, much the same way as a real crime scene contains DNA traces of people.'
So it seems that, for the authors of this proposal, accessing a website, or using the internet for any purpose at all, makes one a virtual criminal. What will they think of next?
But it's even worse ... there's a "third key" ...
Microsoft's newest version of Windows, billed as the most secure ever, contains several serious flaws that allow hackers to steal or destroy a victim's data files across the Internet or implant rogue computer software.
The FBI is asking for access to a massive database that contains the private communications and passwords of the victims of the Badtrans Internet worm. Badtrans spreads through security flaws in Microsoft mail software and transmits everything the victim types. ... [T]he worm replicates by sending copies of itself to all other email addresses found on the host's machine, and installs a keystroke-logger capable of stealing passwords ... The FBI wants indiscriminant access to the illegally extracted passwords and keystrokes of over two million people without so much as a warrant.
A federal judge on Friday [2001-09-07] ordered prosecutors to show him documents next week describing how a classified FBI computer spying system works, saying their argument the system should be kept secret from defense attorneys was "gobbledygook." ... During its 1999 investigation [of Nicodemo Scarfo], the FBI obtained a search warrant to secretly install a "key logger device" on the computer ... The government is resisting the disclosure, claiming the system is classified and that revealing it would endanger national security. But when prosecutors presented an affidavit on Friday from a high-level Justice Department official exhorting the system's classified status, U.S. District Court Judge Nicholas Politan said it was gibberish. ... " It says the guides (that define classified material) are even secret. ..." he said.
The surveillance bill granting the U.K. government sweeping powers to access e-mail and other encrypted Internet communications passed its final vote in the House of Commons on Wednesday and is set to become law on October 5 [2000].
| Cryptosystem ME6 | |
| Encryption and Security | Hermetic Systems Home Page |